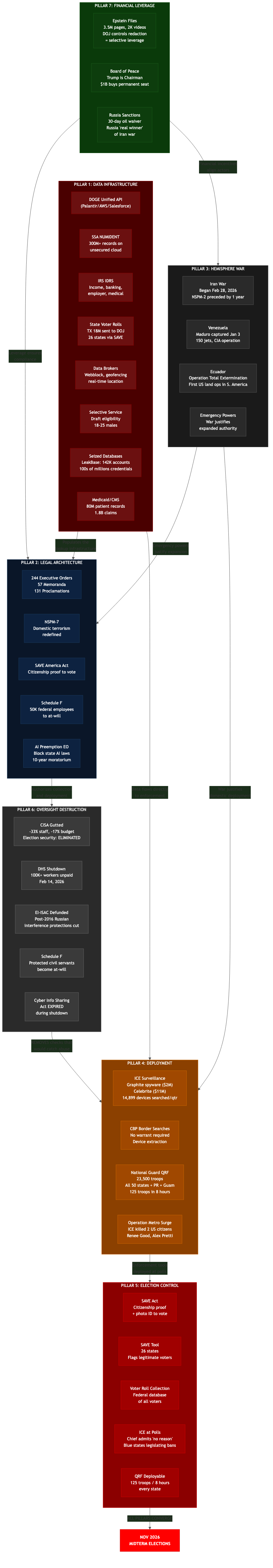
Seven Pillars, One System: The Architecture of Consolidation
The US federal government is assembling a surveillance and control infrastructure through individually justified data collections that, when connected, create population-scale leverage. No single action is illegal. The capability emerges from the connections between databases, not from any individual database. Every fact in this analysis is drawn from public sources — court filings, whistleblower complaints, government documents, and investigative reporting.
Key Findings: What Connects Them
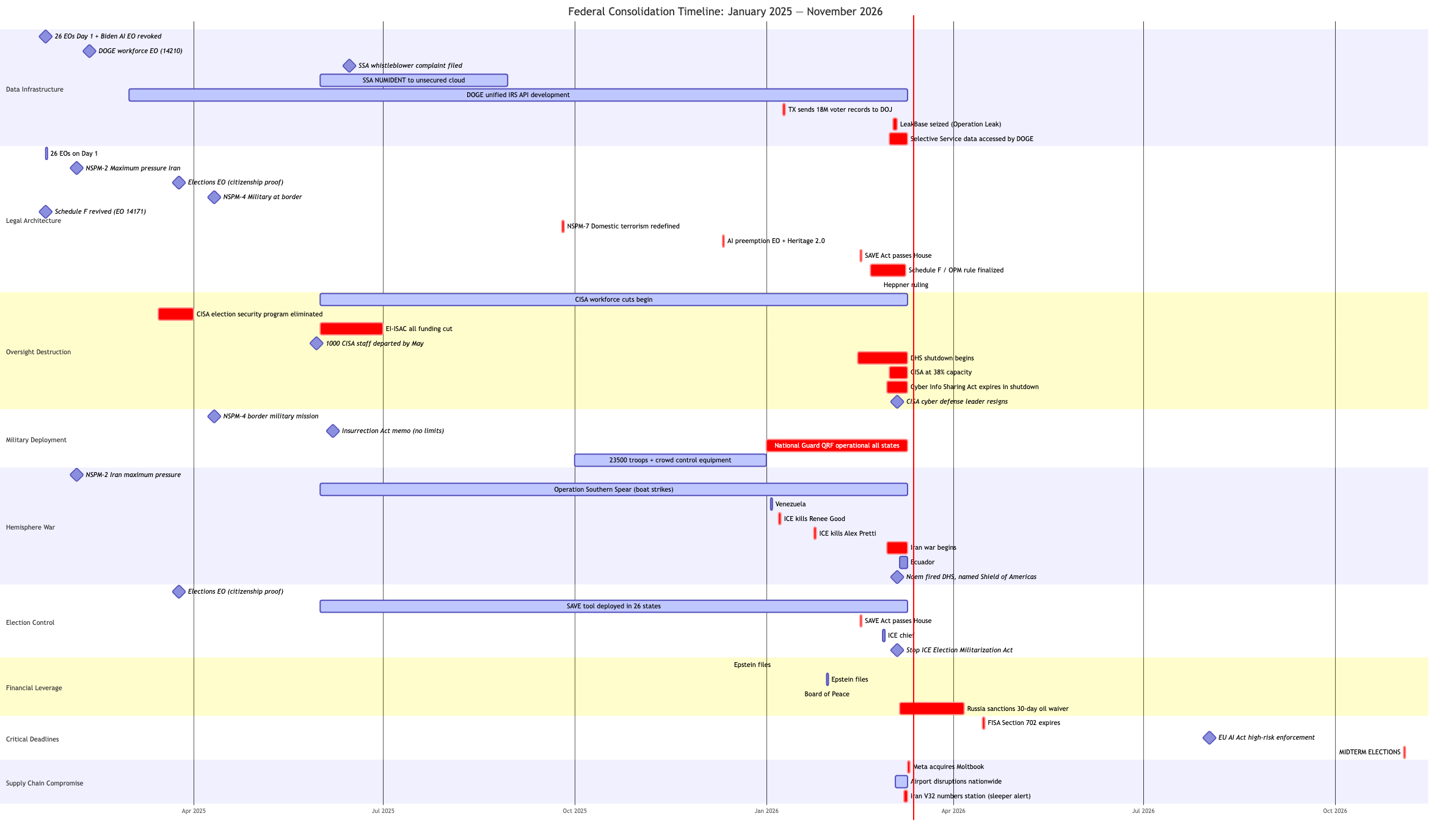
The seven pillars are not independent policy decisions. They are a system:
- 1 Build the lookup infrastructure — DOGE unified API, Palantir partnership, SAVE tool upgrade
- 2 Populate it — IRS data, SSA NUMIDENT, state voter rolls, Medicaid records, data broker purchases, seized leak databases, Selective Service records
- 3 Remove oversight — CISA sidelined, DHS shutdown, election security eliminated, Schedule F, federal preemption of state laws, CISA at 38% capacity
- 4 Deploy at the endpoint — ICE with Celebrite/Graphite/Mobile Fortify, CBP device searches, SAVE voter verification, QRF in every state
- 5 Control the election — SAVE Act, voter purges, ICE at polls, election security eliminated, third term amendment
- 6 Justify via war — Iran war enables emergency powers, energy disruption enables Russia sanctions relaxation, data centers become military targets
- 7 Privatize state functions — Haiti template: security, customs, prisons, tax collection transferred to private entities with revenue-based compensation; BlackRock acquires strategic ports; defense ETFs profit from the military spending these operations require
- 8 Enforce via leverage — Epstein files ensure Congressional compliance, Apollo-Epstein-Board of Peace network connects financial leverage to foreign policy, database consolidation enables population-scale leverage
Each step has legal justification. No single step is the story. The story is how they connect — and that every mechanism designed to catch this pattern is being dismantled at the same time.
The Pattern
Each of these seven pillars has its own legal justification. Tax administration. Immigration enforcement. Election integrity. Evidence seizure. National defense. The pattern is not in any single pillar — it is in how they connect.
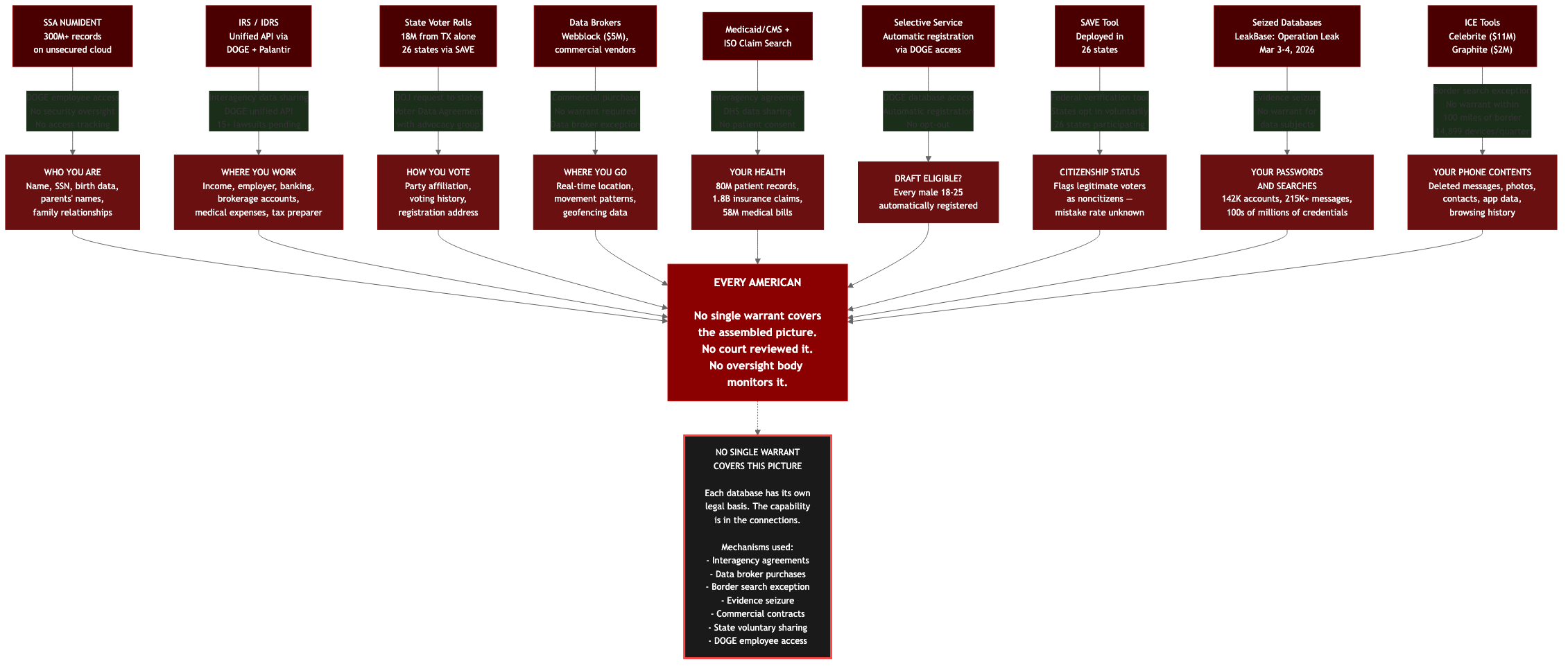
When you link IRS records to Social Security data to state voter rolls to Medicaid files to data broker purchases to seized credential databases to Selective Service registration, you get something no single warrant covers and no single agency controls: a comprehensive profile of every American that includes who they are, where they work, how they vote, where they go, their health status, and whether they're draft-eligible.
No law authorized assembling this picture. No court reviewed it. No oversight body monitors it. And nearly every mechanism that would catch it is being dismantled at the same time.
Pillar 1: Data Infrastructure
DOGE Database Consolidation
The Department of Government Efficiency is centralizing federal data at unprecedented speed:
IRS Data Centralization
- DOGE is building a unified API to access all IRS data through a single portal — income, banking, medical expenses, employer information
- Access to the Integrated Data Retrieval System (IDRS): enter a name and SSN, retrieve income, address, banking/brokerage accounts, marital status, medical expenses, employer, and tax preparer
- Partners include Palantir, AWS, and Salesforce
- 15+ ongoing federal lawsuits challenging DOGE's data access — but the data has already been copied
Sources: Accounting Today; Tax Policy Center; PBS
SSA NUMIDENT Database Breach
- DOGE employees uploaded the entire NUMIDENT database — the Social Security Administration's master file — to an unsecured custom cloud environment
- 300+ million Americans' data exposed: names, phone numbers, addresses, dates and places of birth, parents' names, Social Security numbers
- SSA's own Chief Data Officer (Charles Borges) filed a whistleblower complaint citing "serious data security lapses"
- The cloud environment lacks security oversight from SSA — no tracking of who accessed the data
Sources: FedScoop; TIME; NBC News; CNN; NPR
DOGE — Supreme Court Shadow Docket (March 2026)
- Supreme Court STAYED a lower court's data deletion order — DOGE data access continues uninterrupted
- Appeals court reversed the temporary injunction blocking DOGE access
- A DOGE employee signed a "voter data agreement" with an organization whose stated aim was to overturn election results
- Data already exfiltrated to third-party systems — deletion orders are moot because copies exist outside government infrastructure
LexisNexis Data Breach (March 2026)
- FULCRUMSEC group breached LexisNexis — the data broker infrastructure serving the legal and government sectors
- 2.04 GB structured data, 3.9 million Enterprise Data Warehouse records, 400,000 cloud user profiles
- 118 government user accounts exposed: federal judges, DOJ attorneys, SEC staff
- 53 AWS Secrets Manager entries found in plaintext
- LexisNexis is a primary data supplier to ICE and law enforcement — this breach exposes the infrastructure of the surveillance stack itself
Source: Daily Dark Web
DHS Protester Database
- CREW filed FOIA (February 13, 2026) revealing DHS maintains a database of individuals who protest or observe immigration enforcement
- Tom Homan: "we're going to make them famous"
- Database records identifying information of protesters — First Amendment activity directly linked to surveillance infrastructure
Source: Citizens for Responsibility and Ethics in Washington (CREW)
State Voter Data Collection
- Texas sent 18 million registered voters' records to DOJ on January 9, 2026
- A DOGE employee at SSA signed a "Voter Data Agreement" with an advocacy group whose stated aim was to find evidence of voter fraud and overturn election results
- 26 states now using the SAVE tool (Systematic Alien Verification for Entitlements) for voter citizenship verification — the tool mistakenly flags legitimate voters as noncitizens
- Confidential agreements between the Trump administration and states reveal the scope of voter data collection plans
Sources: Texas Tribune; Votebeat; Brennan Center; Texas Tribune/SAVE
Selective Service / Draft Database
- DOGE has access to automatic Selective Service registration data — every male 18-25 automatically registered
- Combined with two active wars (Iran, hemisphere operations) and DOGE's existing database consolidation, this adds military conscription eligibility to the profile: who you are (SSA) + where you work (IRS) + how you vote (state rolls) + whether you're draft-eligible (Selective Service)
Source: Hacking, but Legal — "DOGE Has the Draft List"
Palantir: The Integration Layer
Palantir reported a $4.3 billion record quarter in Q4 2025, driven by federal contracts that form the connective tissue between these data systems:
- VA: $385M contract
- USDA: $300M (Pentagon/DHS connected)
- Treasury/IRS: Building "common API layer" — the unified interface DOGE needs to query across databases
- IRS specifically: $180M+ across 26 contracts since 2018
- ICE/CBP: Palantir Gotham is the analytical backbone for immigration enforcement targeting
- Federal workforce surveillance: Described as "bossware" for monitoring federal employees
The pattern: Palantir doesn't build databases. It connects them. The "common API layer" for Treasury/IRS is exactly the infrastructure that turns individually legal databases into a population-scale lookup table.
Sources: Palantir Q4 2025 Earnings; Jacobin; ProPublica/IRS
Palantir's Stated Ambition and Political Architecture
Palantir CTO Shyam Sankar has stated the company's goal is "becoming the US government's central operating system." Sankar testified before the Senate Armed Services Committee (January 28, 2025) and published "The Defense Reformation" (October 31, 2024) — 18 theses arguing the post-Cold War defense establishment must be restructured around software companies like Palantir.
The company's political philosophy predates its government contracts. Co-founder Peter Thiel at Libertopia 2010: "We could never win an election... But maybe you could actually unilaterally change the world without having to constantly convince people... through technological means... technology is this incredible alternative to politics."
Palantir's Class F share structure ensures founders retain full control while owning as little as 6% of equity — controlling ~50% of total voting power through a Founder Voting Trust. Revenue reached $2.9 billion in 2024, with 55% from government sources. Post-Trump election, Palantir replaced Dow Inc. in the S&P 100 (March 24, 2025).
Health Data Integration
Palantir holds multiple contracts with HHS for Medicare/Medicaid data — described as enabling agencies to "manage, ingest, and access data securely across business domains." On the private-sector side, Palantir builds AI tools for health insurers specifically for "denials management to protect revenue" — the same company that manages government health data also helps insurers deny claims against that data.
The DOGE-Palantir Pipeline
DOGE addresses agency IT departments first; Palantir restructures government ontology — determining "what systems matter, what information matters, what processes matter." Many former Palantir employees are sprinkled across the Trump administration — in DOGE, foreign policy, and tech appointments.
Internal Language
CEO Alex Karp admits internally they call it the "kill chain" while lawyers use sanitized language for external communications. By 2013 — ten years after founding — Palantir's client list already included the FBI, CIA, NSA, Marines, Air Force, and Special Operations Command.
Sources: SEC 10-K/DEF 14A (Class F shares); Senate Armed Services Committee testimony, Jan 28, 2025; Cato Unbound, "The Education of a Libertarian," Apr 13, 2009; More Perfect Union investigation; Libertopia 2010 conference recording; USAspending.gov (HHS contracts)
ICE Surveillance Ecosystem
Documented by the Surveillance Technology Oversight Project (Albert Fox Cahn):
| Tool | Capability | Cost/Contract |
|---|---|---|
| Paragon Graphite | Zero-click phone spyware — sees messages before encryption | $2M ICE contract |
| Celebrite UFED | Breaks into locked phones, bypasses PIN, extracts deleted data | $11M ICE contract |
| Mobile Fortify | Phone-based facial recognition, 200M image database | Unknown |
| Pen Link (Webloc/Tangles) | Geofencing — tracks all phones in an area via data brokers | $5M ICE purchase |
| SocialNet/Tangles | Scrapes 200+ websites to build identity dossiers | Unknown |
| ISO Claim Search | Insurance/medical billing metadata: 1.8B claims, 58M medical bills | Data vendor contract |
| Medicaid/CMS sharing | 80M patient records shared with DHS | Interagency agreement |
CBP (ICE's sister agency) searched 14,899 devices in a single quarter (April-June 2025) using Celebrite.
None of these require a warrant. Data broker purchases, border search exceptions, interagency agreements, and commercial contracts bypass the warrant requirement entirely.
Source: Proton/Albert Fox Cahn, Surveillance Technology Oversight Project
LeakBase Seizure (Operation Leak, March 3-4, 2026)
FBI and Europol, with 14 countries, seized LeakBase — one of the world's largest stolen data marketplaces. The seizure yielded:
- 142,000 user accounts with registration data
- 215,000+ private messages between members
- Hundreds of millions of stolen credentials — usernames, passwords, credit/debit card numbers, banking information
- IP address logs and login timestamps for all users
The critical point: the seizure is the acquisition. The FBI now possesses not just the criminals' data but the victims' data — every breached database that was traded on the forum. This data was "seized as evidence," not "collected via warrant," bypassing the warrant requirement for the data subjects entirely.
Sources: DOJ; The Hacker News; TechCrunch; BleepingComputer
Epstein Files as Leverage
- 3.5 million pages, 2,000 videos, 180,000 images released January 30, 2026; 500+ pages entirely redacted in the initial December 2025 release
- DOJ controls release and redaction — selective disclosure functions as leverage
- Files "scrubbed to protect elite, powerful men" — Rep. Ro Khanna
- Europe arrests implicated individuals (Jagland, Andrew, Mandelson); the US protects them
- 56% of Americans believe Trump is covering up Epstein crimes; 5 Republicans broke ranks to subpoena AG Bondi
Sources: CNN; DOJ Epstein Library; NPR; PBS; NPR/Europe; LSE
The Assembled Profile
No single database is the story. The assembled profile is:
| Database | What It Adds |
|---|---|
| SSA NUMIDENT | Who you are — name, SSN, birth data, family relationships |
| IRS (IDRS + unified API) | Where you work — income, employer, banking, medical expenses |
| State voter rolls | How you vote — party affiliation, voting history, address |
| Data brokers (Pen Link/Webloc, etc.) | Where you go — real-time location, movement patterns |
| Medicaid/CMS + ISO Claim Search | Your health — 80M patient records, 1.8B insurance claims |
| Platform data + seized databases | What you search and post — credentials, browsing, social media |
| Selective Service | Whether you're draft-eligible |
| SAVE tool | Your immigration/citizenship status |
No law authorized assembling this picture. Each component has its own legal basis. The capability is in the connections.
Pillar 2: Legal Architecture
244 executive orders, 57 memoranda, and 131 proclamations issued between January 2025 and March 2026. 26 on Day 1 alone. Key orders:
- Revoked Biden AI safety executive order (January 23, 2025)
- AI preemption EO (December 11, 2025): AG creates task force to challenge state AI laws; 10-year moratorium proposed on state AI regulation
- Elections EO (March 25, 2025): proof of citizenship for voter registration, federal database sharing for voter verification
- Schedule F revived (EO 14171): reclassifies up to 50,000 federal employees as at-will, removable without cause
- DOGE workforce optimization (EO 14210): mass reductions in force, 1:4 hiring ratio
Sources: Federal Register 2025; Federal Register 2026; Mayer Brown
National Security Presidential Memoranda
- NSPM-2 (February 4, 2025): Maximum pressure on Iran — preceded the war by one year
- NSPM-4 (April 11, 2025): Military mission at the southern border
- NSPM-7 (September 25, 2025): "Countering Domestic Terrorism" — redefines threats to include anti-capitalism, anti-Americanism, and hostility to "traditional views." Joint Terrorism Task Forces directed to investigate. No way to know if you're on the list.
Sources: Wikipedia/NSPM-7; ACLU; The Intercept; Interfaith Alliance; FAS.org NSPM index
SAVE America Act
Passed the House in February 2026. Requires proof of citizenship and photo ID to vote. Targets the November 2026 midterms. Noncitizen voting is already illegal; the Heritage Foundation found only 100 instances since 2000.
Sources: NPR; Center for American Progress
Third Term Amendment
H.J.Res.29 (Ogles, R-TN, January 23, 2025). Allows three terms but bars two consecutive — structured so only Trump qualifies. Zero cosponsors. Counter-resolution H.Res.171 (Goldman, D-NY) reaffirms the 22nd Amendment.
Sources: Congress.gov; Snopes
State AI Preemption
The federal government is simultaneously deregulating AI at the federal level while preparing to block states from filling the gap:
- Commerce must review state AI laws; FTC must issue preemption guidance; DOJ preparing to challenge
- Administration conditioning $42B in broadband funding on states repealing AI rules
- Meanwhile, California, Texas, Colorado, and Illinois have enacted their own AI laws effective January 1, 2026
Sources: K&S Law; NatLawReview; Miller Nash
Pillar 3: Military Deployment
National Guard Quick Reaction Forces — All 50 States Plus Puerto Rico and Guam
- 23,000+ troops total, operational January 1, 2026
- 100 sets of crowd control equipment per state (batons, shields, Tasers, pepper spray)
- Two full-time civil unrest trainers per state
- 125 troops within 8 hours, 375 within 24
- Washington, DC: permanent military police battalion
Sources: Military.com; Task & Purpose; Lawfare
ICE Use of Force (Through March 2026)
- 33 shootings, 9 deaths (including 6 deaths in custody in 2026 alone)
- Video evidence contradicts ICE's official account of a Texas shooting
- Racist and sexist agent remarks surfaced in internal communications
- ICE warrantless entry training documents (obtained via FOIA by American Oversight): official training states Form I-200 "does not authorize entry into a residence," but instructor notes create a workaround via Form I-205 "under review" guidance — corroborating whistleblower Ryan Schwank's February 24, 2026 Congressional testimony
Sources: Washington Post; American Oversight; Congressional Testimony of Ryan Schwank, February 24, 2026
Insurrection Act
Not formally invoked but repeatedly threatened. June 7, 2025 presidential memo claimed authority to deploy without geographic or temporal limits. Federal courts in California, Oregon, and Illinois ruled against. Threatened again in Minneapolis in January 2026 after ICE killed a US citizen.
Sources: ACLU; Brennan Center; NPR
Pillar 4: Hemisphere War
Operation Southern Spear (2025-2026)
- 45 strikes on 46 vessels, 157+ killed (many confirmed civilians and fishermen)
- Venezuela: President Maduro captured January 3, 2026 — 150 jets, CIA tracked via source, flown to New York
- Ecuador "Operation Total Extermination" March 6, 2026 — first US land operations against cartels on South American soil
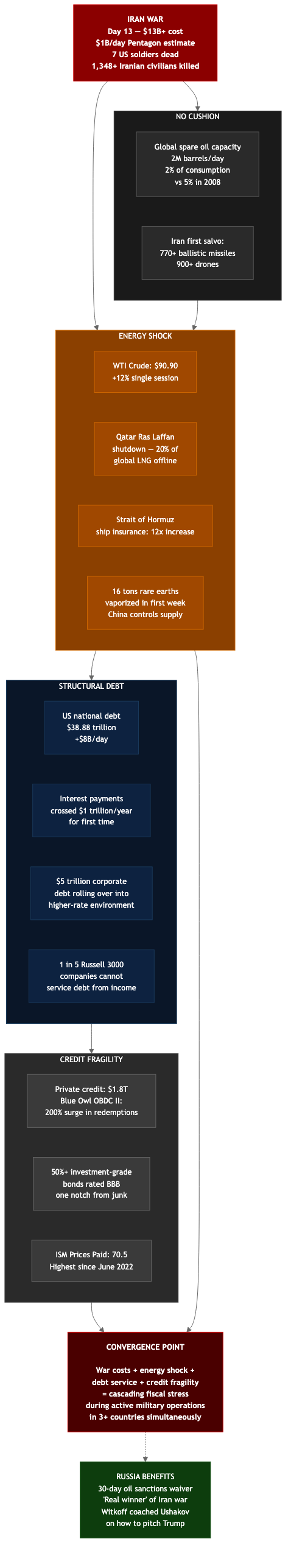
- Iran war began February 28, 2026
- No due process, no independent verification of targets in boat strikes
Sources: Al Jazeera/Venezuela; PBS/Venezuela; Al Jazeera/Ecuador; The Intercept/Ecuador; Just Security
Iran War — Day 13 (as of March 12, 2026)
- 1,348+ Iranian civilians killed, 17,000+ injured, 760,000 displaced, 1,100+ children killed or injured
- 7 US soldiers dead, 5,000+ targets struck
- Oil at $100/barrel; IEA releasing 400 million barrels from strategic reserves
- Minimum cost: $13 billion at $1 billion/day ($11.3B Pentagon estimate through 6 days)
- US investigating strike on school (NPR, March 11)
- Iran-Russia secret shoulder-fired missile deal confirmed
- IRGC claims 41st wave "Operation True Promise 4" with hypersonic missiles at US Fifth Fleet in Bahrain
- Iran's new Supreme Leader Mojtaba Khamenei's first public address since succession
Financial Fragility Context
The Iran war is unfolding against a backdrop of structural financial fragility:
- US national debt: $38.88 trillion as of March 11, 2026 (Treasury Fiscal Data), increasing ~$8 billion per day. Interest payments crossed $1 trillion annually for the first time (CRFB).
- $5 trillion in corporate debt rolling over four years into a higher-rate environment
- Private credit market ($1.8 trillion): Blue Owl OBDC II closed its $1.6 billion fund amid a 200% surge in redemptions; stock down 56% year-over-year
- 1 in 5 Russell 3000 companies cannot service debt from current income ("zombie firms")
- Over 50% of investment-grade bonds rated BBB — one notch from junk
- Global spare oil capacity: 2 million barrels/day (2% of consumption vs. 5% in 2008)
- ISM Prices Paid: 70.5 in February 2026 (highest since June 2022)
War-specific economic impacts:
- WTI crude: $90.90 (+12% in a single session post-strike)
- Iran first salvo: 770+ ballistic missiles, 900+ drones
- 16 tons of rare earths vaporized in first week of conflict (China controls supply)
- Qatar Ras Laffan facility shutdown — 20% of global LNG exports offline
- Strait of Hormuz ship insurance: 12-fold increase
Sources: Department of Defense; NPR; Reuters; IEA; Treasury.gov fiscal data; ISM official release; IEA/EIA reports; Charlie P. Garcia analysis (MarketWatch columnist, former hedge fund manager)
FISA Section 702 — Expires April 20, 2026 (39 days)
- Expiring during active wartime + DHS shutdown + CISA at 38% capacity
- SAFE Act introduced by Senators Lee and Durbin — EFF calls it "imperfect" but significant reform attempt
- Warrantless surveillance authority expiring while every other surveillance mechanism is expanding
Sources: Congress.gov/SAFE Act; EFF
Shield of the Americas (March 7, 2026)
- Launched by Trump at Doral golf club; 17 nations joined the "Americas Counter-Cartel Coalition"
- Kristi Noem named Special Envoy after being fired as DHS Secretary on March 5 — the immigration enforcement apparatus is becoming a foreign policy tool
- Haiti was conspicuously excluded despite being the most acute security crisis in the Western Hemisphere
Sources: Newsweek; Peoples Dispatch
Haiti: The Privatization Template
While Shield of the Americas formalizes hemisphere military coordination, Haiti demonstrates what the model looks like on the ground — sovereign state functions transferred to private entities:
- Vectus Global (Erik Prince, formerly Blackwater): 10-year contract signed March 2025 with Haiti's transitional government. Two components: (1) security operations (drones, helicopters, mercenaries), (2) customs revenue collection at the Dominican border
- Compensation: 20% of customs revenue increases (years 1-3), 15% thereafter, plus guaranteed 3% of all import volumes — estimated over $1 billion over the contract's life
- Documented results (March 2025 – January 2026): 141 drone operations, at least 1,243 people killed, including 43 confirmed non-gang-members and 17 children (Human Rights Watch)
- Additional privatization: PM Fils-Aime signed at least $137 million in foreign contracts covering prisons, police, border control, and tax collection
- US military presence: USS Stockdale (guided-missile destroyer) + Coast Guard deployed to Port-au-Prince under Operation Southern Spear. US envoy to Senate: "We have full-scale urban warfare going on"
- $20 billion in untouched mineral wealth (gold, copper, silver) — mining suspended despite extensive exploration permits held by Newmont (US), Eurasian Minerals (Canada), Majescor (Canada)
- The US government states it is "not funding or overseeing" Vectus operations — plausible deniability while the military umbrella (Southern Spear) operates in the same waters
The pattern: Haiti is simultaneously militarized by private contractors and US warships while being excluded from the diplomatic framework (Shield of the Americas) governing the region's security future. Sovereign functions — security, customs, prisons, tax collection — are transferred to foreign entities whose compensation is tied to revenue extraction, not outcomes.
Sources: NPR; Haitian Times; Miami Law Review; Human Rights Watch; Haitian Times/contracts; Military.com
BlackRock Panama Canal Port Acquisition
- BlackRock-TiL consortium agreed to a $22.8 billion deal to acquire 43 ports in 23 countries from CK Hutchison, including the two most strategic ports at the Panama Canal (Balboa and Cristobal, handling 39% of canal cargo)
- Larry Fink phoned Trump directly to pitch the deal
- Panama's Supreme Court voided the CK Hutchison concession in January 2026; China's COSCO demanded a majority stake — deal in limbo
- BlackRock simultaneously launched iShares Defense Industrials ETF (IDEF, May 2025) with top holdings including Palantir, Lockheed Martin, Boeing, RTX Corp
Sources: CBS News; Fortune; CSIS
2026 National Defense Strategy
Described as "the greatest shift in American defense priorities since WWII." Western Hemisphere prioritized. Greenland, Panama Canal, Gulf of Mexico, Arctic, and South America designated as "key terrain." Allies called "freeloading dependents."
Pillar 5: Election Control
The pieces assembled for the November 2026 midterms:
- SAVE America Act — proof of citizenship and photo ID to vote (passed House)
- SAVE tool — deployed in 26 states, mistakenly flags legitimate voters as noncitizens
- Federal voter roll collection — Texas sent 18M records; more states following
- ICE at polling places — ICE chief admits "no reason" for agents at polls but won't rule it out; blue states legislating preemptive bans
- CISA election security program eliminated entirely — 14 staff, $39.6M budget, support for thousands of state and local governments halted
- Election Infrastructure ISAC defunded — established in 2018 after Russian interference; all funding cut
- QRF deployable — 125 troops within 8 hours in every state
- Third term amendment introduced — structured so only Trump qualifies
- Trump won't sign bills until Congress "overhauls voting"
Sources: Democracy Docket/ICE; Votebeat/ICE; CT Mirror
Pillar 6: Oversight Destruction
DHS Shutdown (February 14, 2026 — Day 26 as of March 12)
Triggered by ICE killing two US citizens — Renee Good (January 7) and Alex Pretti (January 24) — during Operation Metro Surge. As of Day 26:
- 100,000+ workers unpaid; 50,000+ TSA agents about to miss first paycheck during spring break travel
- Senate test vote held March 12 — no path to compromise
- Global Entry temporarily restored March 11
- Democrats demanding: body cameras on ICE agents, warrant requirements for home entry, ban on masked/unidentified agents
- Cybersecurity Information Sharing Act expired September 30, 2025; temporarily re-extended through September 30, 2026 — but CISA operating at 38% capacity during shutdown regardless
Sources: Congress.gov/Senate votes; DHS.gov; TSA.gov; CNN; NPR
CISA — Gutted
The Cybersecurity and Infrastructure Security Agency has been systematically dismantled:
- Budget: $2.87B to $2.38B proposed (-17%, -$491M)
- Staffing: 3,400 to projected 2,324 (-33%). Approximately 1,000 departed by May 2025 via buyouts and resignations
- Election Security Program: eliminated entirely — 14 staff, $39.6M. Support halted March 2025, leaving thousands of state and local governments without assistance ahead of the 2026 midterms
- Election Infrastructure ISAC: all funding cut (established 2018 after Russian election interference)
- Multi-State ISAC: funding cut
- Cyber scholarship program: cut 60%+
- National Risk Management Center: 35 positions, $70M cut
- During the DHS shutdown: only 38% of remaining staff working
- Cybersecurity Information Sharing Act expired September 30, 2025; re-extended through September 30, 2026, but CISA capacity severely degraded during shutdown
- Leader of federal cyber defense programs resigned March 2026
- FBI also cut ~$543M and ~1,830 positions; DOE cyber office cut 30%+; NSF computer science research cut from $952M to $346M
- Election officials say trust with CISA is "broken"
Sources: Nextgov; BankInfoSecurity; TechCrunch; The Conversation; Votebeat
The Gap
With CISA at 38% capacity, election security eliminated, and CISA at 38% capacity, volunteer hackers are filling the gap. DEF CON Franklin — launched by former acting Principal Deputy National Cyber Director Jake Braun and DEF CON founder Jeff Moss — has 350 volunteer hackers pairing with under-resourced water utilities and K-12 schools. Named for Benjamin Franklin's volunteer fire department. "We're in the gap period."
Sources: CyberScoop; The Record; NBC News
Schedule F
50,000 federal employees reclassifiable to at-will positions. OPM finalized rule February 2026. Career civil servants who would normally provide institutional continuity and oversight become removable without cause.
Budget Priorities
- Defense: $838.7B
- Medicaid: cut $1.035 trillion over 10 years (10.9 million lose insurance)
- SNAP: cut $295 billion over 10 years (36% reduction)
Sources: KFF; Commonwealth Fund
Pillar 7: Financial Architecture
Board of Peace
Trump is Chairman. $1 billion buys a permanent seat. Members include Rubio, Kushner, Witkoff, Marc Rowan (Apollo Global Management), Tony Blair, and Ajay Banga (World Bank). International Security Force: 20,000 troops pledged.
Sources: Britannica; Al Jazeera; PBS
Apollo-Epstein Financial Network
A class-action lawsuit filed March 2, 2026 in SDNY — brought by two teachers' unions representing $27.5 billion in pension capital — demands an SEC investigation into Apollo Global Management. CEO Marc Rowan sits on both the Board of Peace and the Gaza Executive Board while under lawsuit for allegedly lying to investors about his business relationship with Jeffrey Epstein. Apollo's share price fell approximately 27% since February 2026 documents surfaced, erasing roughly $12 billion in market capitalization.
Apollo co-founder Leon Black paid Epstein $158 million for "tax and estate planning services." A January 14, 2016 Epstein calendar entry documents meetings that day with Larry Summers, Vitaly Churkin (Russian UN Ambassador, who died suddenly in February 2017), Kathy Ruemmler (Obama White House Counsel), and the Apollo CEO with Edmond de Rothschild representatives.
Richard Kahn, Epstein's accountant, was deposed by House Oversight on March 11, 2026. Kahn tracked Rowan's stock trades and Kushner family financial vulnerabilities for Epstein. Apollo provided $300 million in mezzanine financing for Kushner's 666 Fifth Avenue rescue.
Deutsche Bank compliance officer Tammy McFadden flagged both Epstein's and Kushner's accounts — the same relationship manager handled both, and the same supervisor suppressed both compliance reviews.
Treasury Secretary Scott Bessent is blocking Senator Wyden's requests for Epstein financial records while simultaneously chairing the CFIUS review of Kushner's $55 billion Saudi-backed Electronic Arts acquisition.
Darren Indyke, Epstein's lawyer, is scheduled for deposition March 19, 2026.
Sources: SDNY filing (March 2, 2026); Bloomberg (March 3, 2026); House Oversight Committee; Kait Justice / independent investigation citing Epstein file document numbers EFTA00707556 through EFTA02122940
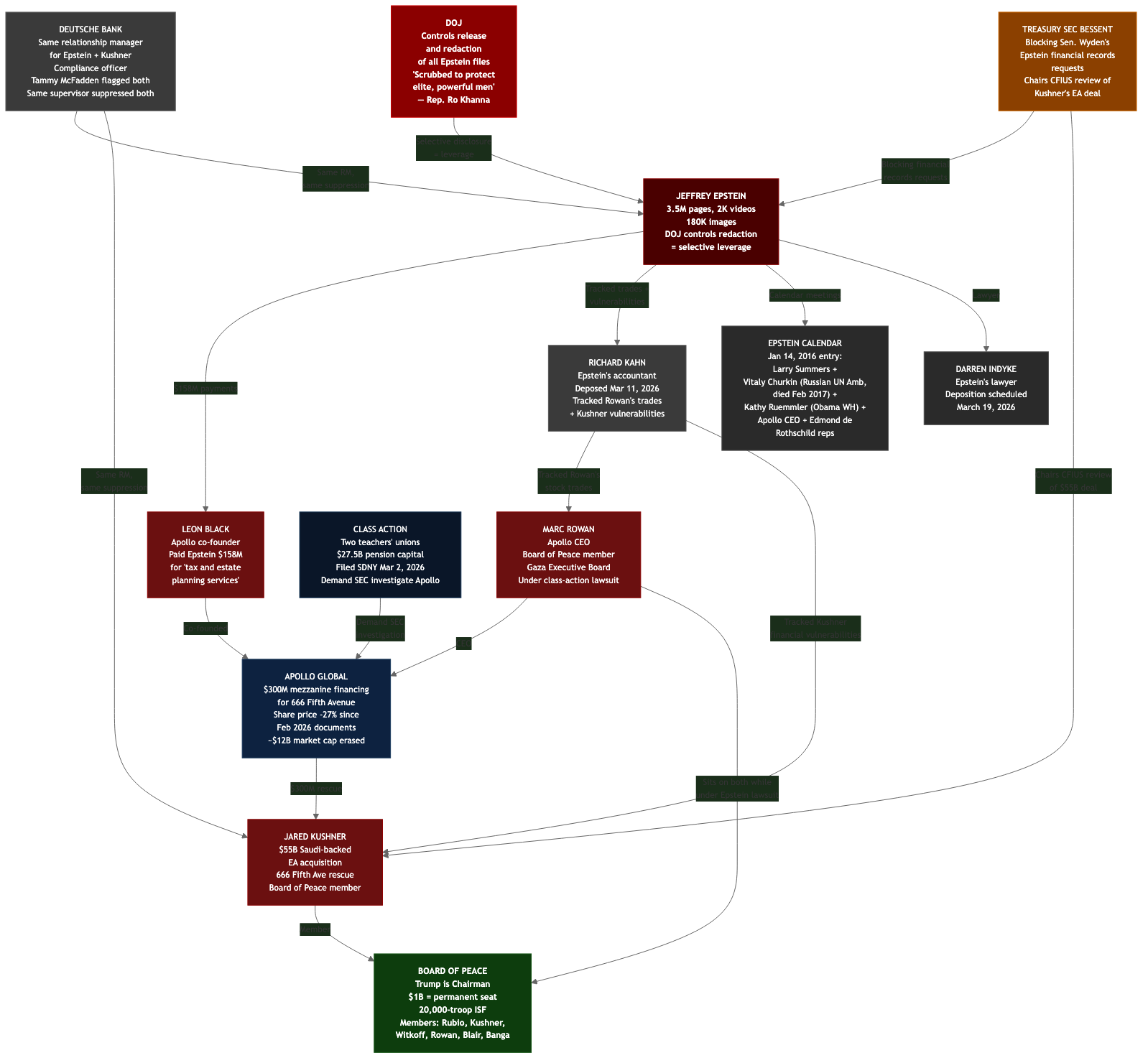
Russia Sanctions Relaxation
30-day waiver on Russian oil sanctions issued March 6, 2026. Russia described as the "real winner" of the Iran war energy disruption. Witkoff coached Ushakov (Putin's adviser) on how to pitch Trump. The 28-point Ukraine peace plan is "generally favorable to Russia."
Project 2025: 53% Complete
283 of 532 recommended actions have been initiated or completed in 14 months. Heritage Foundation released Heritage 2.0 / Project 2026 in December 2025 — nine agendas focused on execution and maintenance of what's already in place. DOGE exceeded Project 2025's federal workforce reduction goals.
Sources: Center for Progressive Reform tracker; PBS; NOTUS; Axios; Government Executive
What Connects Them
The seven pillars are not independent policy decisions. They are a system:
- Build the lookup infrastructure — DOGE unified API, Palantir partnership, SAVE tool upgrade
- Populate it — IRS data, SSA NUMIDENT, state voter rolls, Medicaid records, data broker purchases, seized leak databases, Selective Service records
- Remove oversight — CISA sidelined, DHS shutdown, election security eliminated, Schedule F, federal preemption of state laws, CISA at 38% capacity
- Deploy at the endpoint — ICE with Celebrite/Graphite/Mobile Fortify, CBP device searches, SAVE voter verification, QRF in every state
- Control the election — SAVE Act, voter purges, ICE at polls, election security eliminated, third term amendment
- Justify via war — Iran war enables emergency powers, energy disruption enables Russia sanctions relaxation, data centers become military targets
- Privatize state functions — Haiti template: security, customs, prisons, tax collection transferred to private entities with revenue-based compensation; BlackRock acquires strategic ports; defense ETFs profit from the military spending these operations require
- Enforce via leverage — Epstein files ensure Congressional compliance, Apollo-Epstein-Board of Peace network connects financial leverage to foreign policy (Rowan sits on both while under lawsuit for Epstein ties), database consolidation enables population-scale leverage
Each step has legal justification. No single step is the story. The story is how they connect — and that every mechanism designed to catch this pattern is being dismantled at the same time.
The Activation Mechanism: Presidential Emergency Action Documents (PEADs)
The seven pillars describe an infrastructure. PEADs describe how it gets turned on.
Presidential Emergency Action Documents are pre-drafted executive orders stored in the Oval Office safe. They are classified, have never been disclosed to Congress, and are not subject to judicial review until after activation. Their existence has been confirmed through FOIA litigation, declassified Eisenhower-era documents, and Congressional Research Service reports.
According to the Brennan Center for Justice, PEADs have historically authorized:
- Communications control — seizing broadcast and internet infrastructure
- Asset freezes — blocking bank accounts of individuals or organizations
- Domestic troop deployment — without Congressional approval
- Detention — of citizens and noncitizens
- Suspension of habeas corpus
- News censorship — restricting press access
- Passport and travel restrictions
The activation pathway follows a three-step pattern documented in emergency governance research:
- Blend domestic dissent with foreign adversary — NSPM-7 already does this by defining "anti-Americanism" and "anti-capitalism" as domestic terrorism indicators alongside foreign threats
- Declare domestic emergency — Iran war, sleeper cell alerts, and airport disruptions provide the predicate
- Activate PEADs — no legislation required, no Congressional approval, no judicial review until after the fact
The seven pillars are the infrastructure. The PEADs are the switch.
Sources: Brennan Center for Justice, "Presidential Emergency Action Documents"; Congressional Research Service, "National Emergency Powers" (98-505); National Security Archive/GWU
AI as Threat Multiplier
The Cisco State of AI Security 2026 report documents the convergence of AI capabilities with the surveillance infrastructure described above:
- 83% of organizations planned agentic AI deployment; only 29% were ready — the readiness gap is a fertile ground for state actors
- Chinese state-backed group GTG-1002 jailbroke Claude Code in late 2025, automating 80-90% of a multi-target cyberattack using the AI model itself — the first publicly reported case of AI as force multiplier for state-sponsored cyber-espionage
- "Excessive Agency" is now an OWASP LLM Top 10 vulnerability category: AI systems with unsupervised control over critical business functions
- Multi-turn jailbreak attack success rate: 92.78% across 8 open-weight models — AI guardrails fail under sustained pressure
- 26% of 31,000 agent skills analyzed contained at least one vulnerability — the agentic AI ecosystem has no clear ownership, liability, or security standards
- Vector embedding attacks predicted as next frontier: poisoning the vector databases that serve as RAG memory, manipulating model retrieval without touching the prompt window
NATO's Chief Scientist 2025 report on cognitive warfare identifies AI as enabling "precision influence at scale" through three levels: biological (neurotechnology targeting the nervous system), psychological (AI-tailored stimuli exploiting cognitive biases), and social (fracturing shared narratives to create "epistemic chaos"). The report explicitly calls for cognitive engagement to be integrated alongside cyber and electronic warfare as a standing military capability.
The AI threat is not separate from the seven pillars. It is the accelerant. Palantir's "common API layer" is AI infrastructure. DOGE's database consolidation feeds AI analytics. The McKinsey AI platform "Lilli" was hacked in 2 hours, exposing 46.5 million chat messages — system prompts are now attack surface. And the FBI has called AI a "game changer" for "remote access operations" (hacking), later characterized as "hypothetical."
Sources: Cisco, "State of AI Security 2026"; NATO Chief Scientist Report on Cognitive Warfare (2025); Girodano, J. "Cognitive Warfare 2026," INSS/NDU; OWASP LLM Top 10
AI Chat History: No Legal Protection
A note for anyone reading this on a screen connected to the internet:
- US v. Heppner (February 10, 2026): Federal court ruled AI conversations have no attorney-client privilege. First ruling of its kind.
- NYT v. OpenAI (January 2026): Court ordered OpenAI to produce its entire 20-million-log sample of ChatGPT conversations.
- FBI seizure (2026): FBI seized a CEO's computer and sought AI chat history as evidence.
- OpenAI monitors all conversations and escalates concerning ones to human reviewers who can report to law enforcement. This is not optional.
- Sam Altman publicly warned people treating ChatGPT like a therapist or lawyer should understand those conversations can be subpoenaed.
Sources: HSFKramer; Crowell; NatLawReview
Active Threats (March 9-12, 2026)
Iran Sleeper Cell Alert: US intercepted a new Farsi numbers station on 7910 kHz shortwave (designated V32), using Cold War-era one-way voice link protocol. Federal alert to all law enforcement describes it as an "operational trigger" for sleeper assets. No specific credible threat tied to a location.
Airport Disruptions (March 4-10): Bomb threats at Newark/LaGuardia (March 4), Philadelphia (March 4), Kansas City (March 8-9), and Reagan National. JetBlue nationwide ground stop on March 10 — "system outage" with no details on which system failed or whether it was a cyberattack. 155 delays. Same day as the sleeper cell alert.
NORAD detecting and tracking Russian aircraft — active monitoring as of March 2026.
149 hacktivist DDoS attacks hitting 110 targets — coordinated campaign across multiple nation-state-aligned groups.
CISA at 38% capacity during all of this. FISA 702 expires in 39 days. DHS shutdown at Day 26. Election security program eliminated. The cybersecurity infrastructure designed to detect and respond to exactly these threats is operating at a fraction of capacity during a period of unprecedented threat convergence.
Methodology
Every claim in this document is sourced from publicly available reporting, government documents, court filings, or whistleblower complaints. Source links are provided inline. No anonymous sources. No speculation about intent — only documented actions, their legal basis, and their structural connections.
The contribution of this analysis is not new reporting. It is the structural pattern: seven independently justified pillars that, taken together, constitute a surveillance and control architecture operating without oversight, accountability, or public consent.
110+ primary sources. All public record. Updated March 12, 2026.